Set up VPN site-to-site connection via Microsoft Azure
In the digitalized world of work, mobile work concepts, such as home office and mobile working, are becoming increasingly relevant. The Corona crisis provided an enormous development boost here in recent months. Companies around the world are establishing various models to enable working from home. It is particularly important that all employees are always securely connected to headquarters via a VPN site-to-site connection.
VPN site-to-site connection via Microsoft Azure
With more than 200 products and cloud services, the Microsoft Azure platform offers multiple paths to the cloud. (Source)
The Azure VPN Gateway allows local networks to be connected via site-to-site VPNs. Similar to the normal set up and connect at the corporate site. Cross-site connectivity between local customer environments and Azure is enabled. (Source).
When does a VPN connection make sense? - For an answer, see the latest blog article in our VPN blog series.
Site-to-Site VPN Connection: Azure step-by-step guide
To create a site-to-site VPN gateway connection from on-premise network to the virtual network on Azure, there are few steps to follow:
Step 1: Creating a VPN gateway
Step 2: Creating a local network gateway
Step 3: Configuring your VPN device
Step 4: Creating and verifying a Site-to-Site VPN connection
Step 1: Create a VPN gateway
Type ‘virtual network gateways’ in the search bar and select it. Click on the Create button and use the Virtual network gateway page to configure the required information:
- In the Basic fields select your subscription type, choose a name for your gateway, and select the region in which the gateway will be created (it must be the same location as the virtual network)
- Choose VPN as gateway type and Route-based as VPN type. For SKU you can select Basic, Standard or High-performance type.
- From the dropdown menu select the virtual network (VNet) to which you want to add this gateway. If it is not already configured, specify the gateway subnet address range.
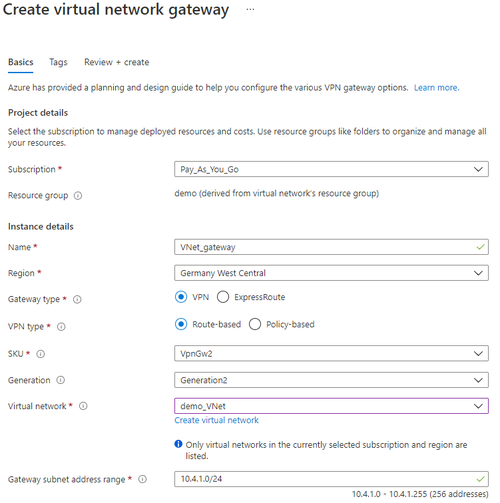
- In Public IP address fields select Create new and give a name to the public IP address instance. Select Review + create and after the successful validation, deploy the VPN gateway by clicking on the Create button.
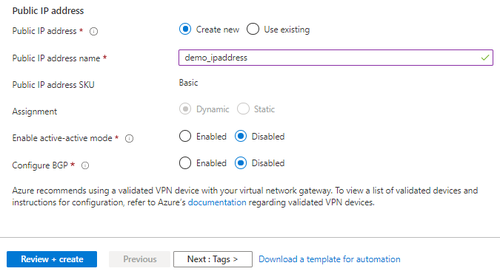
Step 2: Create a local network gateway
Type ‘local network gateways’ in the search bar and select it. Click on the Create button and use the Create local network gateway page to configure the required information:
- Choose a name for your local network gateway and select the endpoint type for the on-premises VPN device (IP address or FQDN).
- You can add one or multiple address space ranges for the network that local network represents.
- Select your subscription type, choose the resource group and the location (it is not required to be the same as VNet’s).
Step 3: Configure your VPN device
- For Site-to-Site network connection, you also need to configure your on-premise VPN device.
- You need to set a shared key which you will use in the step 4 - creating Site-to-Site connection.
- You need to know the public IP address of your virtual network gateway. It can be found in the Overview tab of created VNet gateway.
- It is also possible to download existing VPN device configuration scripts depending on the device you have.
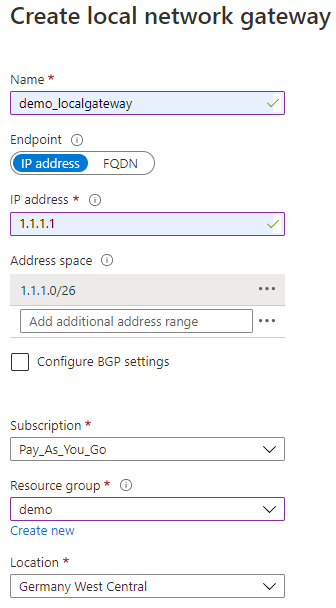
Step 4: Create and verify a Site-to-Site VPN connection
- Open ‘virtual network gateways’ from the search bar results and select your network gateway. Under the settings there is Connections tab where you can add new connection.
- Choose a name for your connection and select Site-to-Site (IPsec) as the connection type.
- As virtual network gateway is already known; you have to select a local network gateway that you want to use.
- Shared key (PSK) must be the same value as the one you set while configuring your on-prem VPN device.
- Both Use Azure Private IP Address and Enable BGP can remain unchecked, and for the IKE Protocol choose IKEv2.
- Subscription, resource group and location should already be fixed, as it depends on previously created virtual and local network gateway. Click OK to create your connection and the Status must be Succeeded after a few moments.
- To verify the created Site-to-Site VPN connection, you can select your virtual network gateway under All resources page and under Connections tab check if the status value is Connected.
Our VPN Site-to-Site Connection blog series includes several posts. Learn how to set up your VPN connection with cloud providers AWS and IBM step-by-step in our next blog article.
Recommended articles
All blog articles